Decrypt Files Encrypted by STOP Ransomware
This is an article, created to explain how you can decrypt files, encrypted by STOP Ransomware virus.
STOP ransomware is the type of malware, whose main idea is to get users to pay ransom in the form of BitCoin to get their files back. Not all variants of this ransomware can be decrypted for free, but we have added the decryptor used by researchers that is often updated with the variants which become eventually decrypted. You can try and decrypt your files using the instructions below, but if they do not work, then unfortunately your variant of the ransomware virus is not decryptable.

STOP Ransomware – More Information
Researchers have categorised STOP ransomware to be of several different variants.
- The variant with the uppercase extensions.
- The Puma variants of STOP.
- The Djvu STOP variants.
The uppercase file extension variants only include uppercase extensions and they are a bit outdated, whie the Puma and Djvu variants are relatively new ones as the Djvu variants being the latest viruses to hit the workd.

How to Decrypt Your Files
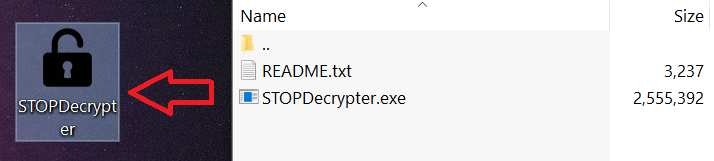
To decrypt your files, first you need to download STOP Decryption tool from Bleeping Computer, available on the URL below:
After the download, make sure to follow these steps:
Step 1) Extract the decrypter somewhere:
Step 2) Run it as an administrator:
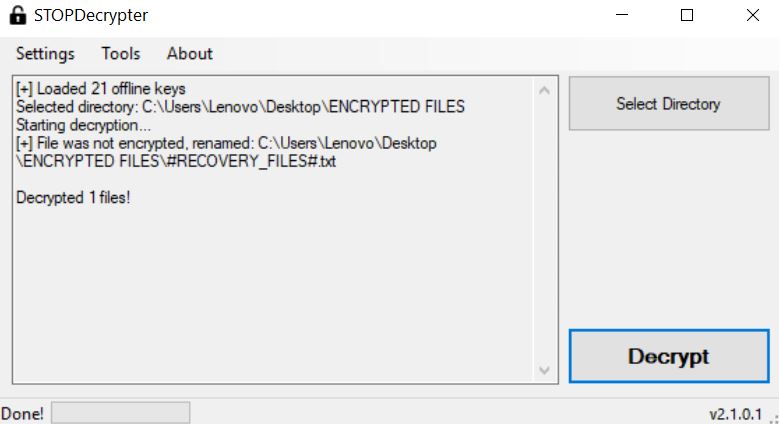
Step 3) Click on “Select Directory” and then select a folder, where your important files are encrypted.
Step 4) Click on Decrypt and be patient. The software will return how many files were decrypted:

Remove STOP Ransomware
Be sure to only remove STOP once your files are decrypted. If the files are not decrypted, you should wait until security researchers update the decryptor to work for your variant. Until then, we strongly recommend that you backup your encrypted files and NOT pay the ransomware. Also, you can try and get some of your files back by following the alternative recovery instructions underneath. They are no guarantee that you will get all your files back, but with their help, you could restore at least some of the files.
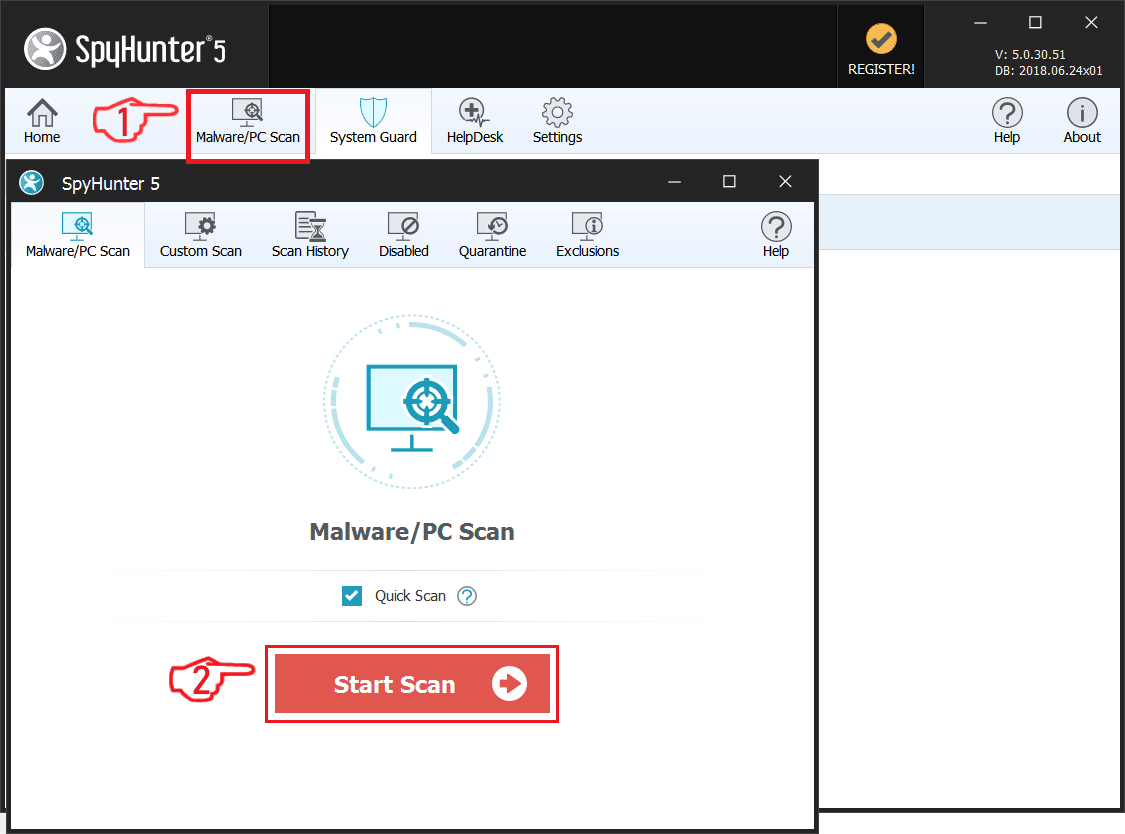
To remove STOP ransomware, you should follow the first two steps. If they do not work, then try to remove this virus automatically with an advanced anti-malware software. Such software is often the preffered removal method, since it aims to detect an delete all STOP files plus remove them.
Preparation before removing STOP Ransomware.
Before starting the actual removal process, we recommend that you do the following preparation steps.
- Make sure you have these instructions always open and in front of your eyes.
- Do a backup of all of your files, even if they could be damaged. You should back up your data with a cloud backup solution and insure your files against any type of loss, even from the most severe threats.
- Be patient as this could take a while.
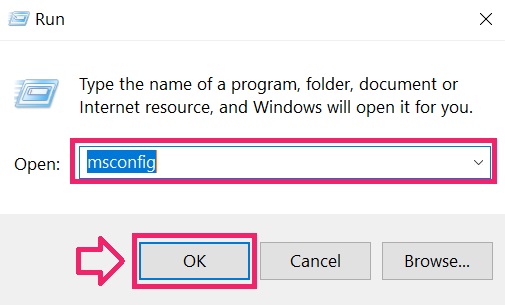
Step 1: Boot Your PC In Safe Mode to isolate and remove STOP Ransomware
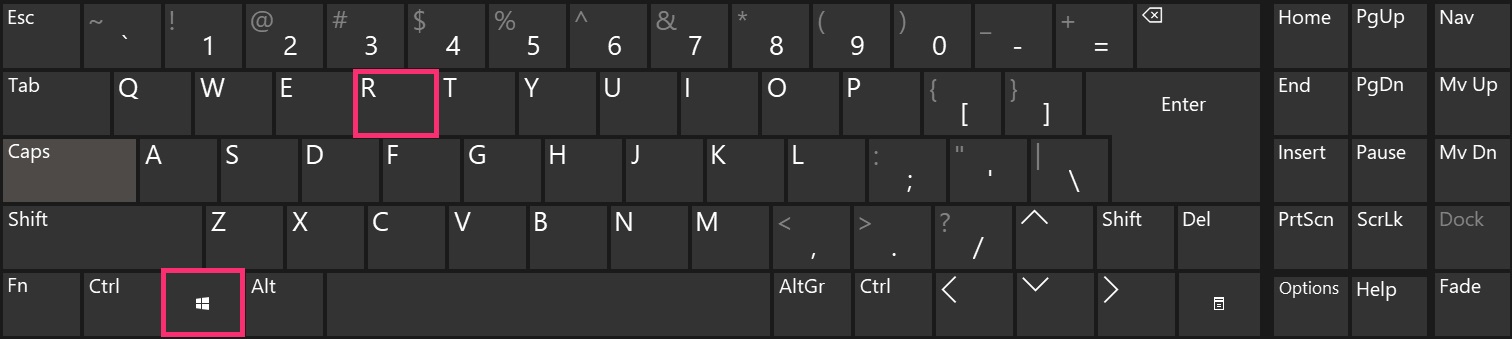

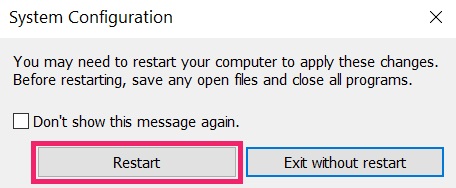

Step 2: Clean any registries, created by STOP Ransomware on your computer.
The usually targeted registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by STOP Ransomware there. This can happen by following the steps underneath:
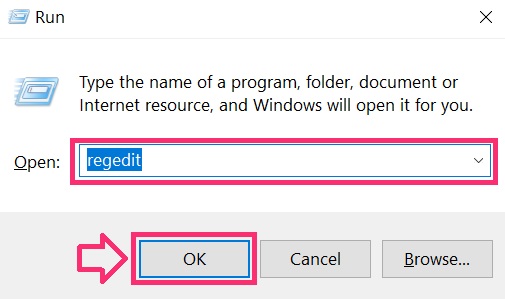
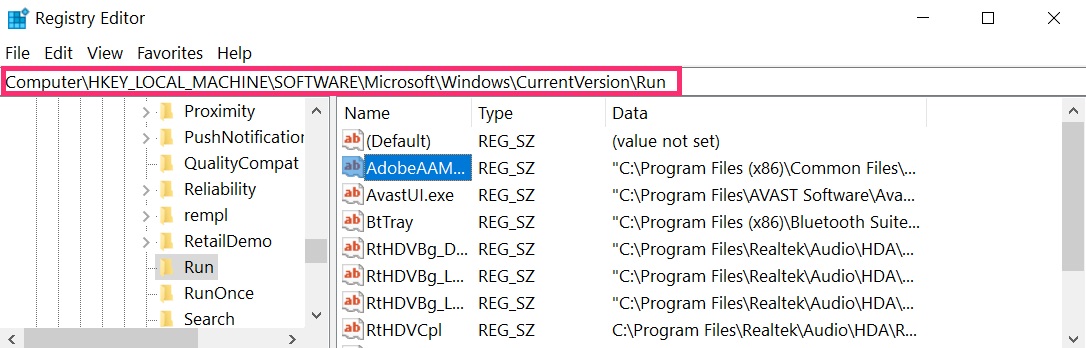
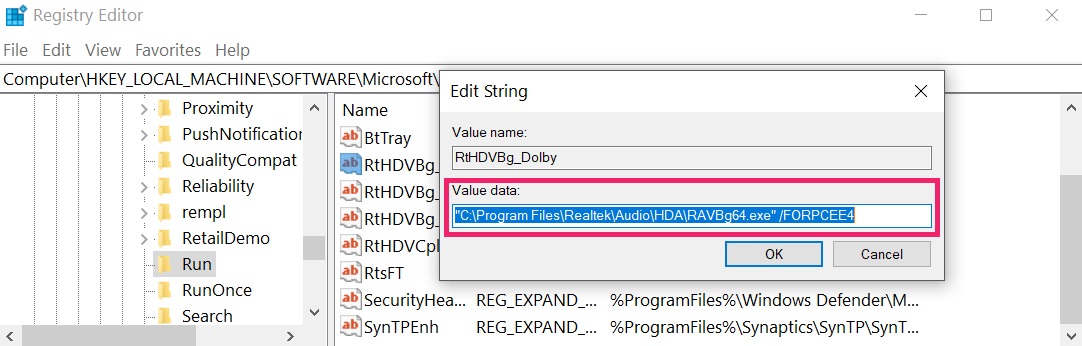 Tip: To find a virus-created value, you can right-click on it and click “Modify” to see which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click “Modify” to see which file it is set to run. If this is the virus file location, remove the value.
Step 3: Find files created by STOP Ransomware
 For Windows 8, 8.1 and 10.
For Windows 8, 8.1 and 10. For Windows XP, Vista, and 7.
For Windows XP, Vista, and 7.
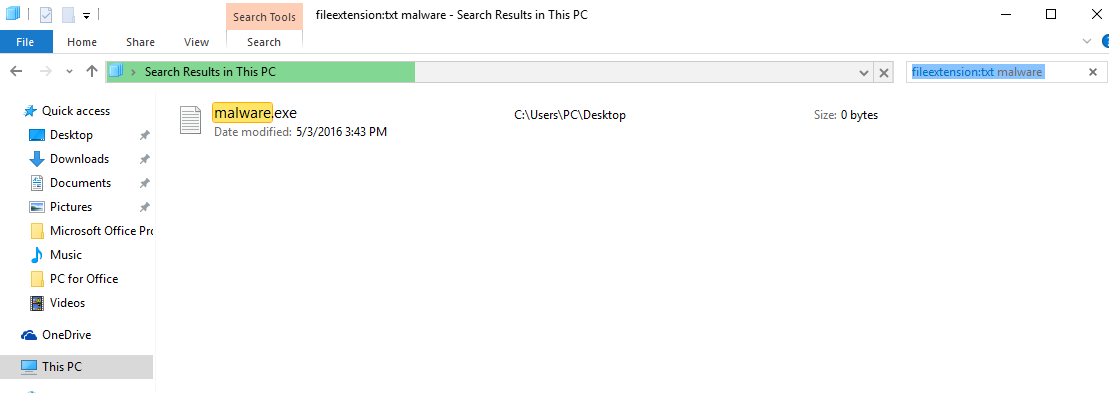
For Newer Windows Operating Systems
1: On your keyboard press + R and write explorer.exe in the Run text box and then click on the Ok button.
2: Click on your PC from the quick access bar. This is usually an icon with a monitor and its name is either “My Computer”, “My PC” or “This PC” or whatever you have named it.
3: Navigate to the search box in the top-right of your PC’s screen and type “fileextension:” and after which type the file extension. If you are looking for malicious executables, an example may be “fileextension:exe”. After doing that, leave a space and type the file name you believe the malware has created. Here is how it may appear if your file has been found:
N.B. We recommend to wait for the green loading bar in the navination box to fill up in case the PC is looking for the file and hasn’t found it yet.
IMPORTANT!
Before starting “Step 4”, please boot back into Normal mode, in case you are currently in Safe Mode.
This will enable you to install and use SpyHunter 5 successfully.
Before starting “Step 4”, please boot back into Normal mode, in case you are currently in Safe Mode.
This will enable you to install and use SpyHunter 5 successfully.
Step 4: Scan for STOP Ransomware with SpyHunter Anti-Malware Tool
Step 5 (Optional): Try to Restore Files Encrypted by STOP Ransomware.
Ransomware infections and STOP Ransomware aim to encrypt your files using an encryption algorithm which may be very difficult to decrypt. This is why we have suggested several alternative methods that may help you go around direct decryption and try to restore your files. Bear in mind that these methods may not be 100% effective but may also help you a little or a lot in different situations.
Method 1: Scanning your drive’s sectors by using Data Recovery software.
Another method for restoring your files is by trying to bring back your files via data recovery software. Here are some suggestions for preferred data recovery software solutions:
Another method for restoring your files is by trying to bring back your files via data recovery software. Here are some suggestions for preferred data recovery software solutions:
- Stellar Data Recovery Technicians License(Pro version with more features)
- Stellar Windows Data Recovery
- Stellar Photo Recovery
Method 2: Trying Kaspersky and EmsiSoft’s decryptors.
If the first method does not work, we suggest trying to use decryptors for other ransomware viruses, in case your virus is a variant of them. The two primary developers of decryptors are Kaspersky and EmsiSoft, links to which we have provided below:
If the first method does not work, we suggest trying to use decryptors for other ransomware viruses, in case your virus is a variant of them. The two primary developers of decryptors are Kaspersky and EmsiSoft, links to which we have provided below:
Method 3: Using Shadow Explorer
To restore your data in case you have backup set up, it is important to check for Volume Shadow Copies, if ransomware has not deleted them, in Windows using the below software:
Method 4: Finding the decryption key while the cryptovirus sends it over a network via a sniffing tool.
Another way to decrypt the files is by using a Network Sniffer to get the encryption key, while files are encrypted on your system. A Network Sniffer is a program and/or device monitoring data traveling over a network, such as its internet traffic and internet packets. If you have a sniffer set before the attack happened you might get information about the decryption key. See how-to instructions below:







No comments